Cybersecurity, in its simplest terms, is the practice of protecting our online presence - including personal information, data, and digital systems - from various cyber threats. It’s like the digital equivalent of a robust lock system protecting our homes.
As we continue to share more of our lives online, from financial transactions to personal communications, the importance of cybersecurity only grows. For those passionate about making a tangible difference in the fight against cybercrime, becoming a digital forensic investigator is an intriguing career path. This specialized role combines advanced technical skills with investigative techniques to analyze and recover data, track cybercriminal activities, and ensure justice in the digital realm.
There are myriad examples of rigid cybersecurity systems, from multi-factor authentication protocols to complex encryption algorithms. Such systems work tirelessly behind the scenes to protect us from potential threats, such as identity theft, phishing scams, and malicious software.
However, while these systems provide a robust first line of defense, it’s crucial to remember that we, as users, have a significant role to play in our online safety.
In the following sections, we will delve deeper into the realm of cybersecurity, providing you with key tips and considerations to help fortify your online experience. Remember, the digital world can be as hazardous as it is convenient – stay vigilant, stay safe.
Understanding Cybersecurity
The journey to understanding cybersecurity begins with acknowledging the various forms cybersecurity threats can take. These threats range from viruses and malware designed to exploit weaknesses in a system and compromise its integrity to social engineering tactics like phishing scams that manipulate individuals into revealing sensitive information. Acknowledging these threats is the first step in developing an effective cybersecurity strategy.
 Image by macrovector on Freepik
Image by macrovector on Freepik
A comprehensive approach to cybersecurity goes beyond using antivirus software or a firewall. It involves a holistic approach that includes not only technological measures but also education and awareness, policy and procedural measures, and a robust incident response plan.
Some of the biggest industries in the world are heavily reliant on cybersecurity measures to protect their assets and customers. One such industry is the casino industry, which has seen a massive shift towards online platforms in recent years. As more people turn to online casinos for entertainment and gambling, robust cybersecurity systems become crucial for safeguarding sensitive information and preventing fraud. They include measures like secure connections, data encryption, and strict authentication protocols – all working together to ensure a safe and fair online gaming experience. The FanDuel Casino Games are prime examples of a platform that goes above and beyond to protect its players’ privacy and security.** **
Potential Cyber Threats
The realm of potential cyber threats is vast and constantly evolving. A common and particularly insidious threat is Identity Theft, where cybercriminals steal personal information such as names, social security numbers, and bank details. They then use this information to commit fraud, often with devastating results for the victims.
 Image by Freepik
Image by Freepik
Another widespread threat is Phishing scams. Typically, these scams involve bogus emails or texts that appear to be from credible sources. They aim to trick individuals into revealing sensitive information, such as passwords or credit card numbers.
A third category of threats falls under Malicious Software or Malware. It’s an umbrella term for various harmful software types, including viruses, worms, ransomware, and spyware. Malware can damage or disrupt digital systems, steal sensitive data, or give cybercriminals access to your systems.
Remember, these are just a few examples. The landscape of cyber threats is vast and constantly changing, which underscores the importance of staying informed and vigilant.
User’s Role in Cybersecurity
In the fight against cyber threats, users are the first line of defense. Maintaining personal cyber hygiene practices is as essential as the advanced cybersecurity measures put in place by organizations. One such practice is the regular updating of software and applications. These updates often contain patches for newly discovered security vulnerabilities that, if left unaddressed, can serve as entry points for cybercriminals.
Another crucial aspect of personal cyber hygiene is password management. Users are encouraged to use strong, complex, unique passwords for each of their online accounts and to change these passwords regularly. Implementing multi-factor authentication, where available, adds an additional layer of security.
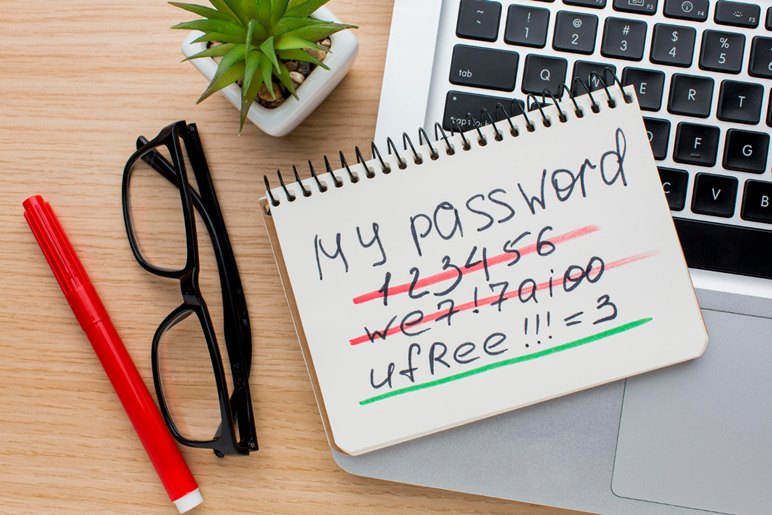 Image by Freepik
Image by Freepik
Furthermore, users should be vigilant when clicking on links or opening attachments, particularly those received from unknown sources. These could potentially be phishing attempts or contain malicious software.
Lastly, users should be cautious when sharing personal information online and only do so on secure and trusted platforms. By understanding and implementing these practices, users can significantly contribute to their cybersecurity and the overall health of the digital ecosystem.
Key Tips and Considerations for Enhancing Cybersecurity
Here are some key tips and considerations for enhancing your cybersecurity:
- Regular Updates: Keep all your software, including your operating systems and applications, up-to-date.
- Strong Passwords: As already mentioned, use unique, complex passwords for all your accounts. Consider using a password manager, which can generate and store strong passwords for you.
- Multi-Factor Authentication: Whenever possible, enable multi-factor authentication. It adds an extra layer of protection, as it requires more than one method of verification.
- Secure Networks: Avoid using public Wi-Fi for sensitive transactions. If you need to use a public network, use a trusted virtual private network (VPN) to encrypt your data.
- Be Suspicious: Always be cautious of unsolicited communications and links. If something seems off, it probably is.
- Backups: Keep regular backups of your important data. In case of a ransomware attack or failure of your hardware, backups can help you recover your data.
Consequences of Negligent Cybersecurity Practices
Negligent cybersecurity practices can lead to dire consequences, ranging from personal to financial and reputational damage. Personal privacy implications are one of the most immediate and acute effects.
Sensitive information such as credit card numbers, social security numbers, and private communications can be compromised, leading to Identity Theft and other forms of fraud.
Moreover, it can result in significant financial risks. Cyber attacks often lead to direct financial loss due to fraud or ransom demands. Indirect costs may include legal fees, regulatory fines, and the cost of repairing damaged systems.
 Image by krakenimages.com on Freepik
Image by krakenimages.com on Freepik
Reputational damages are another critical consequence. A cyber attack can undermine customers’ trust in a business or organization, leading to a loss of customers, partners, and revenue. Restoring a damaged reputation can be a long and costly process. Therefore, prudent cybersecurity practices are not just about avoiding negative consequences but also preserving trust, safety, and integrity in the digital world.
Read also: 4 Strategies for Effective Third-Party Risk Management in Business
Final Thoughts
In the digital age, cybersecurity is a shared responsibility. It calls for a collective effort from technology providers, organizations, and individual users. As we continue to embrace digital transformation, prioritizing cybersecurity is essential. Keeping abreast of emerging threats, diligently following best practices, and fostering a culture of security can all contribute to a safer digital ecosystem. Remember, a secure digital world does not just protect our present; it also paves the way for a future where technology can be leveraged without fear. Let’s all play our part in making this vision a reality.

